Are you looking to grant someone access to your network but unsure how to formalize it? Crafting a permission authorization letter is a straightforward process that ensures clarity and security for all parties involved. In this guide, we'll walk you through a simple template that captures all the essential details and conveys your trust in the individual accessing your network. So, if you're ready to streamline your authorization process, keep reading to explore the full article!
Letter Template For Network Access Permission Authorization Samples
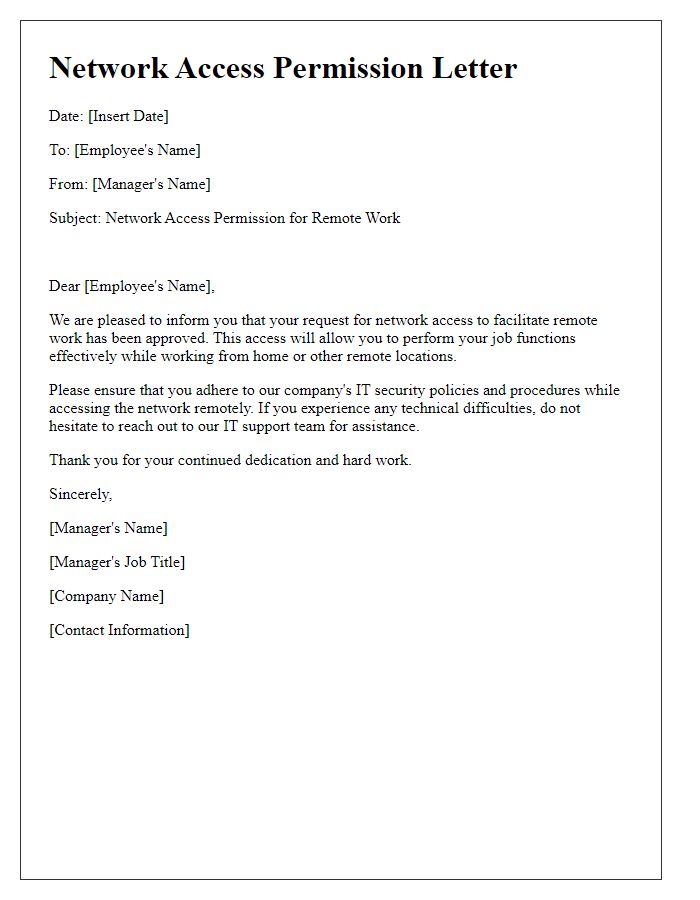
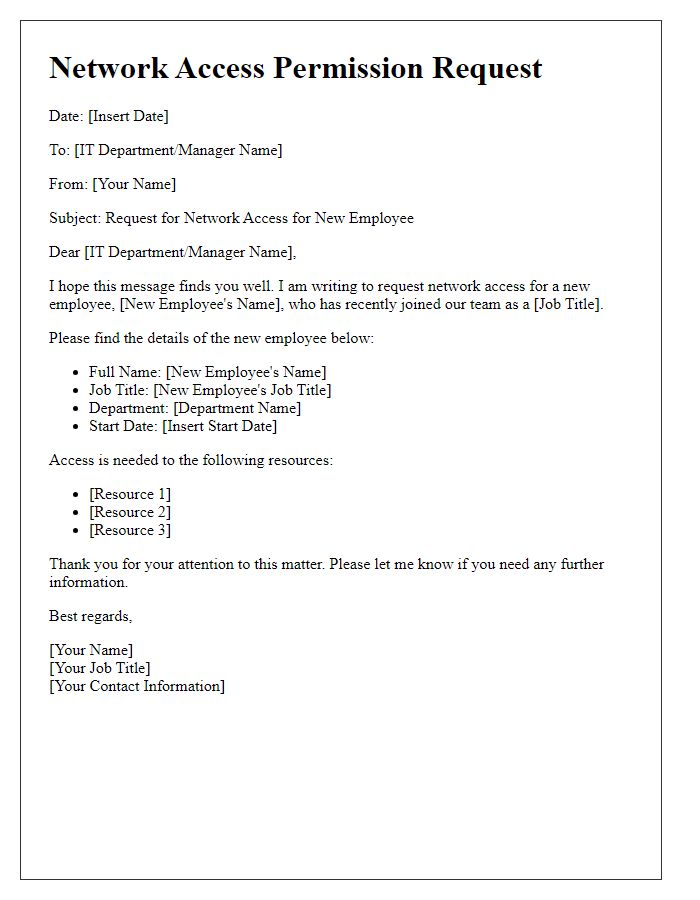
Letter template of network access permission for remote work considerations
Purpose of Network Access
Network access authorization requests, particularly within corporate environments, often serve the crucial purpose of ensuring secure connectivity for employees. This process facilitates access to a company's internal systems, applications, and resources, such as databases and intranet services, vital for daily operations. For instance, accessing the company's Virtual Private Network (VPN) allows remote employees to connect securely while protecting sensitive data from unauthorized access. Organizations often require this authorization to maintain compliance with industry regulations, such as the General Data Protection Regulation (GDPR), which mandates the protection of personal data. Each request typically specifies the user's role, the type of access needed, and the duration of access, ensuring accountability and traceability within the network structure.
Specific Access Requirements
When seeking network access permission for an organization, specific access requirements play a crucial role in ensuring security and efficiency. These requirements typically include user identification (such as employee ID, full name, and department) and necessary permissions defined according to role specifications within the company's digital framework. Organizations might implement different access levels, like administrative access for IT staff, restricted access for regular employees, and guest access for visitors. Compliance with data protection regulations, such as the General Data Protection Regulation (GDPR), is essential throughout the authorization process to safeguard sensitive information. Additionally, network monitoring protocols may be established to track user activity and flag potential threats, promoting a secure network environment within headquarters or remote offices.
Duration of Access Needed
Network access permission authorization is essential for users requiring connectivity to secure networks. This authorization typically specifies the necessary duration of access. For instance, a temporary access period may range from a few hours to several days, contingent on the user's needs such as attending a conference at the Javits Center, New York City, lasting three days. Alternatively, a long-term access duration could span months for employees working on continuous projects like software development or data analysis. Requesting appropriate timeframes ensures compliance with security protocols while meeting operational requirements. Clear documentation of start and end dates, along with the purpose of access, aids network administrators in effectively managing permissions.
Individual/Department Responsible
In corporate environments, obtaining network access permission is crucial for ensuring information security and operational efficiency. The individual or department responsible for managing network access typically handles the authorization process, evaluating requests from employees. This department, often known as Information Technology (IT) or Network Administration, establishes protocols for granting access based on job roles, responsibilities, and security classifications of data being accessed. Specific guidelines outline the criteria for approval, including user authentication via secure methods such as two-factor authentication, and compliance with organizational security policies. Effective communication between the requesting individuals and the responsible department ensures a streamlined process while safeguarding sensitive data across corporate networks.
Security and Compliance Measures
Access to secure networks requires strict compliance with security protocols. Organizations often mandate authorization letters for network access permissions. These letters typically outline the purposes for access, stipulate user responsibilities, and detail security measures necessary to prevent data breaches. Specific compliance standards, such as GDPR (General Data Protection Regulation) or HIPAA (Health Insurance Portability and Accountability Act), may be referenced to underline legal obligations and ensure data protection. Additionally, the role of IT security teams in monitoring network activity is emphasized, to maintain the integrity and confidentiality of sensitive information. Any breach of these protocols could result in disciplinary actions or legal repercussions for employees, reinforcing the importance of adherence to organizational security policies.

Comments