Greetings! In today's ever-evolving landscape of security threats, understanding the results of a security audit is vital for maintaining the integrity of your organization. A well-structured letter detailing these results not only communicates findings effectively but also fosters a culture of transparency and trust. Whether you're addressing stakeholders or your internal team, clear communication is key to ensuring everyone is on the same page regarding necessary improvements and action plans. Ready to dive deeper into crafting the perfect security audit letter? Let's explore the essential components together!
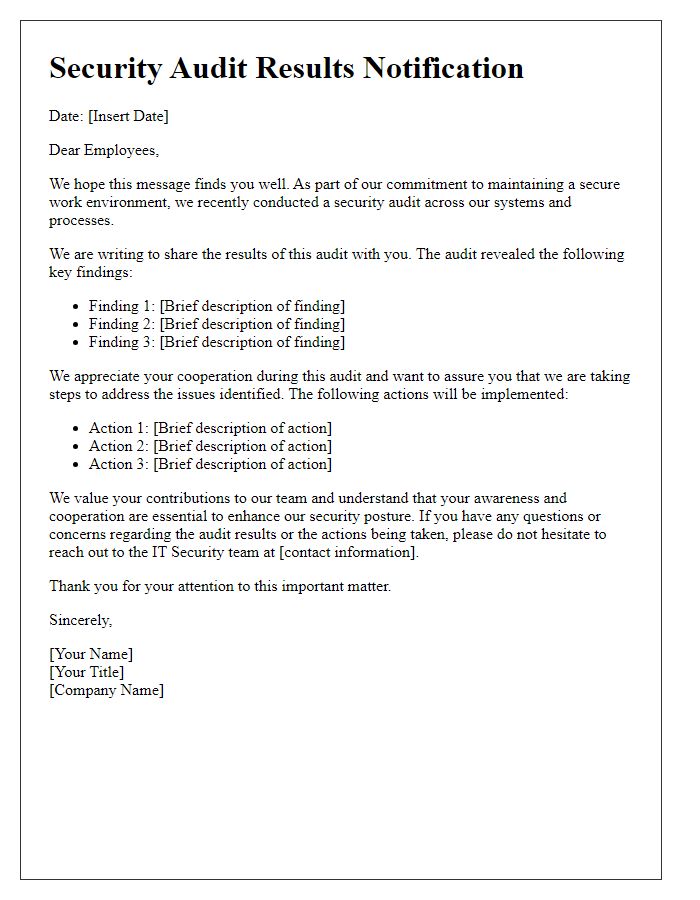
Letter Template For Security Audit Results Samples
Executive Summary
The security audit results highlight significant vulnerabilities within the organization's information systems, particularly in the areas of network security and data management. The audit conducted in July 2023 by an external firm assessed policies, procedures, and technical controls across multiple departments in compliance with ISO 27001 standards. Key findings indicate that 40% of servers, located in the primary data center in San Francisco, are not compliant with current security protocols, increasing risks of data breaches. Additionally, unpatched software vulnerabilities were identified on critical applications used by over 500 employees, leading to potential exploitation by cybercriminals. Recommendations include immediate implementation of a security patch management system and enhanced employee training programs to address human factors in security. Rectifying these issues is paramount to safeguarding sensitive client information and maintaining regulatory compliance.
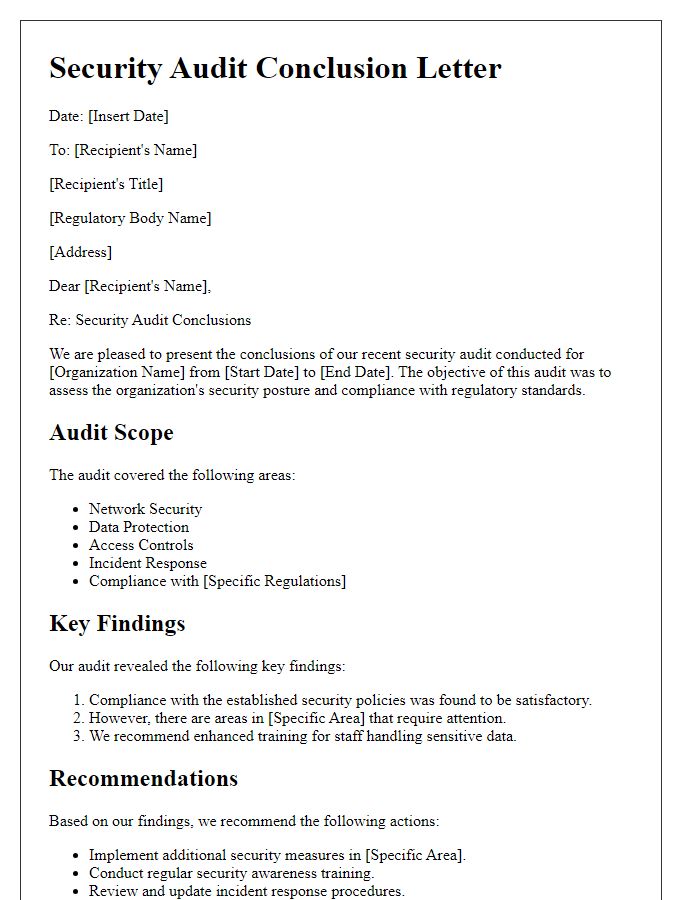
Audit Scope and Methodology
A comprehensive security audit is essential for assessing vulnerabilities and ensuring compliance with regulations in organizations, especially in sectors like finance, healthcare, and technology. The audit scope typically encompasses various domains such as network infrastructure, application security, and physical access controls, covering all critical assets and data repositories. Methodology often includes techniques like penetration testing, vulnerability scanning, and policy reviews, implemented through frameworks such as NIST SP 800-53 or ISO/IEC 27001. The engagement usually involves data gathering via interviews and documentation reviews, alongside automated tools for continuous monitoring. Clear delineation of audit boundaries ensures focused examination of identified risks, facilitating effective remediation and enhancing overall security posture.
Key Findings and Observations
The security audit results reveal several critical findings regarding data protection measures across the organization. Unauthorized access attempts were logged (approximately 150 attempts in Q2 2023), indicating potential vulnerabilities in the network perimeter defenses. Additionally, the audit identified that 60% of servers, particularly those hosting sensitive client information, lacked up-to-date security patches, exposing them to risks from known exploits. Furthermore, employee training records indicated that only 40% of staff completed cybersecurity awareness courses, which may contribute to phishing susceptibility. Data encryption practices were inconsistent, affecting 30% of stored personal data in the database, increasing the risk of exposure in case of a breach. Finally, the lack of multi-factor authentication (MFA) on critical systems further heightened the risk, as it reduces the effectiveness of conventional password protection.
Risk Assessment and Impact
Security audits uncover vulnerabilities that can compromise data integrity, confidentiality, and availability within an organization. A comprehensive risk assessment identifies potential threats, such as cyberattacks, insider threats, and system failures. For example, the likelihood of a ransomware attack has increased by 150% over the last two years, indicating a serious risk for many sectors, including healthcare and finance, which manage sensitive information. The impact of such breaches can be severe, leading to financial losses estimated at $1.85 million for small to medium-sized enterprises and reputational damage that can take years to recover from. Additionally, regulatory non-compliance, especially with laws like GDPR or HIPAA, can result in fines upward of $20 million or 4% of annual revenue. Overall, thorough risk assessment paired with effective mitigation strategies is essential to safeguard organizational assets and maintain stakeholder trust.
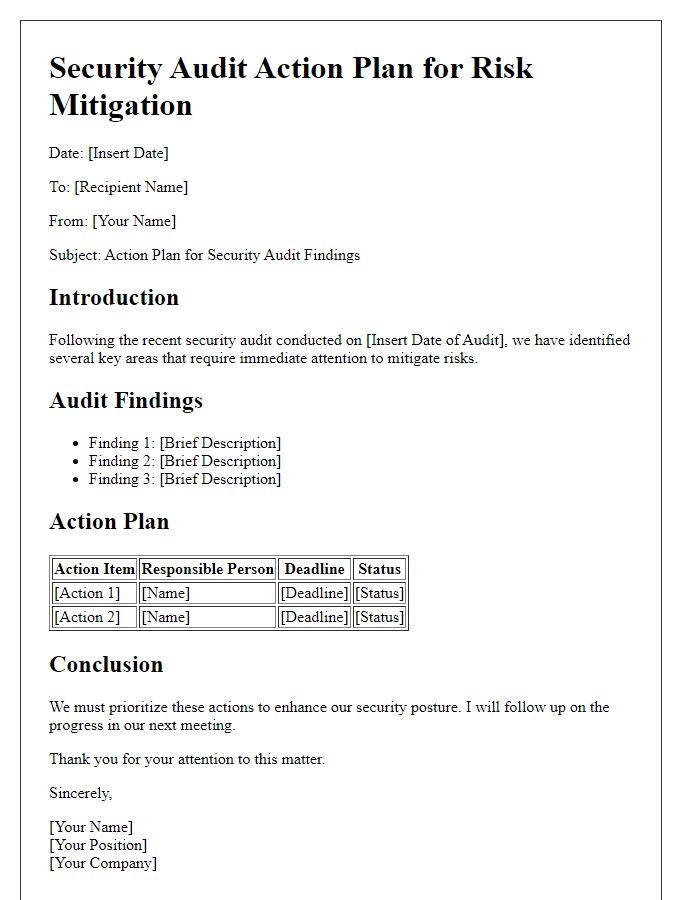
Recommendations and Action Plans
A comprehensive security audit reveals critical vulnerabilities within the organization's IT infrastructure, requiring immediate attention. The audit, conducted by CyberSecure Evaluators in October 2023, identified significant risks including outdated software applications, which could expose sensitive data. Specifically, the outdated version of the company's customer relationship management (CRM) system, known as ClientConnect 5.2, has not received necessary security patches since January 2022. It is recommended to prioritize the upgrade to ClientConnect version 6.0, which includes enhanced encryption protocols and regular updates. Additionally, increasing employee cybersecurity awareness through scheduled training sessions is vital, especially focusing on phishing tactics, as studies show that 90% of data breaches originate from human error. Regular network monitoring, using advanced intrusion detection systems like SecureGuard Pro, should be implemented to preemptively identify potential breaches. Action plans must be outlined and executed within the next quarter to achieve a more secure operational environment.

Comments